Never-before-seen Linux malware gets installed using 1-day exploits

Researchers have unearthed Linux malware that circulated in the wild for at least two years before being identified as a credential stealer that’s installed by the exploitation of recently patched vulnerabilities.
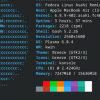
The newly identified malware is a Linux variant of NerbianRAT, a remote access Trojan first described in 2022 by researchers at security firm Proofpoint. Last Friday, Checkpoint Research revealed that the Linux version has existed since at least the same year, when it was uploaded to the VirusTotal malware identification site. Checkpoint went on to conclude that Magnet Goblin—the name the security firm uses to track the financially motivated threat actor using the malware—has installed it by exploiting “1-days,” which are recently patched vulnerabilities. Attackers in this scenario reverse engineer security updates, or copy associated proof-of-concept exploits, for use against devices that have yet to install the patches.
Checkpoint also identified MiniNerbian, a smaller version of NerbianRAT for Linux that’s used to backdoor servers running the Magento ecommerce server, primarily for use as command and control servers that devices infected by NerbianRAT connect to. Researchers elsewhere have reported encountering servers that appear to have been compromised with MiniNerbian, but Checkpoint Research appears to have been the first to identify the underlying binary.