Security vulnerabilities in ISC BIND 9
Credit:
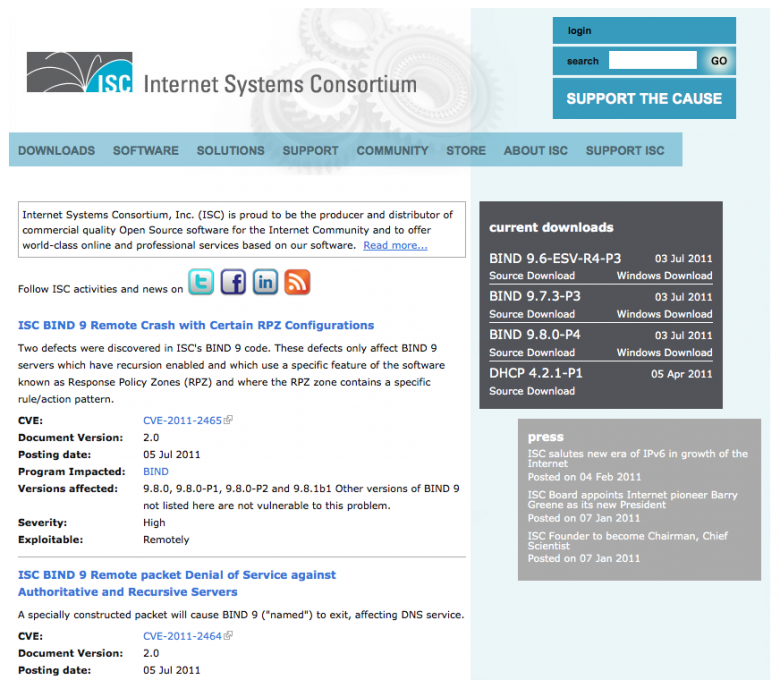
https://www.isc.org/
Internet Systems Consortium today released two new security advisories detailing a couple of newly found security issues within ISC BIND 9.
A defect in the affected versions of BIND could cause the "named" process to exit when queried, if the server has recursion enabled and was configured with an RPZ zone containing certain types of records. Specifically, these are any DNAME record and certain kinds of CNAME records.
The patch release of BIND 9.8.0-P4 alters the behavior of RPZ zones by ignoring any DNAME records in an RPZ zone, and correctly returning CNAME records from RPZ zones









































































