Password cracking experts decipher elusive Equation Group crypto hash
Unraveling a mystery that eluded the researchers analyzing the highly advanced Equation Group the world learned about Monday, password crackers have deciphered a cryptographic hash buried in one of the hacking crew's exploits. It's Arabic for "unregistered."
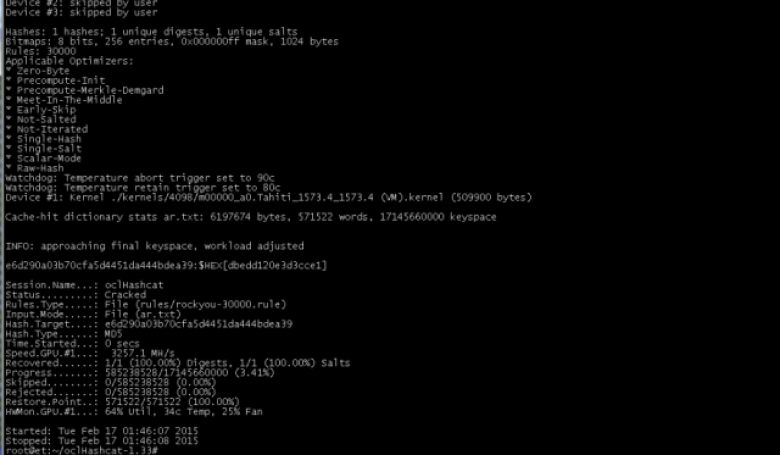
Researchers for Moscow-based Kaspersky Lab spent more than two weeks trying to crack the MD5 hash using a computer that tried more than 300 billion plaintext guesses every second. After coming up empty-handed, they enlisted the help of password-cracking experts, both privately and on Twitter, in hopes they would do better. Password crackers Jens Steube and Philipp Schmidt spent only a few hours before figuring out the plaintext behind the hash e6d290a03b70cfa5d4451da444bdea39 was غير مسجل, which is Arabic for "unregistered." The hex-encoded string for the same Arabic word is dbedd120e3d3cce1.
"That was a shock when it popped up and said 'cracked,'" Steube told Ars Monday evening. He is the developer behind the free Hashcat password-cracking programs and an expert in password cracking.