Military chip crypto cracked with power-analysis probe
German computer scientists have taken advantage of the powerful number-crunching abilities of graphics chips to demonstrate a practical attack on the encryption scheme in programmable chips.
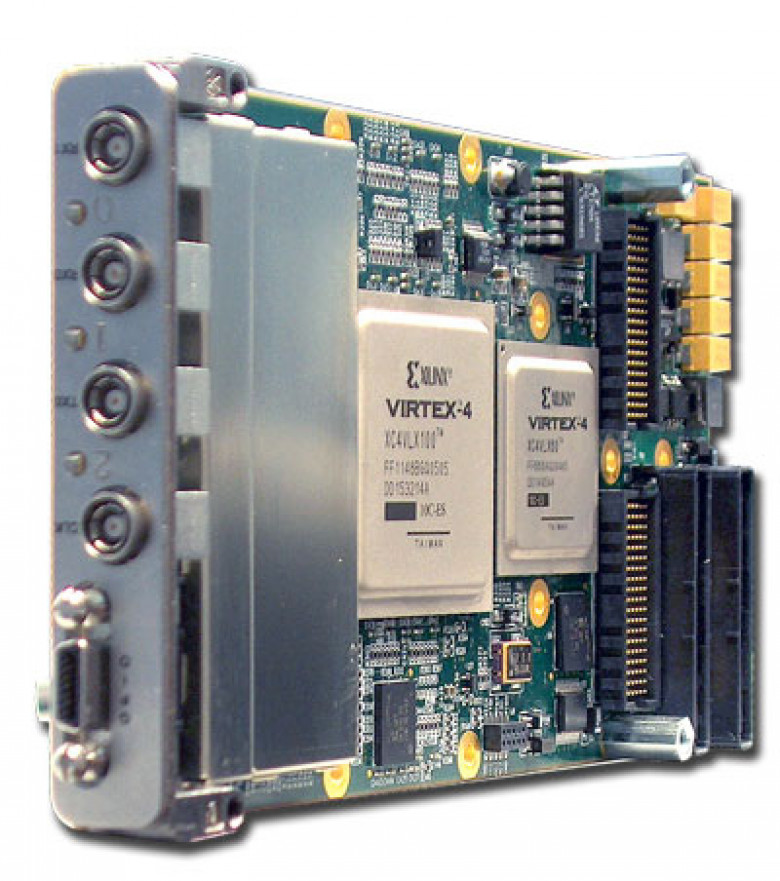
Field Programmable Gate Array (FPGA) chips of the type used in embedded systems belonging to the military and the aerospace industry are vulnerable to attacks based on analysing power usage during the power up sequence of the chip. The side-channel attack against the bitstream encryption mechanism used by Virtex 4 and Virtex 5 chips from Xilinx allowed researchers from the Ruhr University to extract a key used to decrypt configuration instruction files. The technique uncovered secret keys by analysing fluctuations in power consumption during the decryption process.
Only one power up sequence needs to be monitored. The subsequent number crunching took up to nine hours, in the case of the more advanced Virtex 5 chip, or six hours in the case of the earlier Virtex 4. The approach is akin to listening to the clicks coming from the tumblers of a safe to work out a combination, but using variations in power consumption rather than sound.