Jon Oberheide says latest Android will be "pretty hard" to exploit
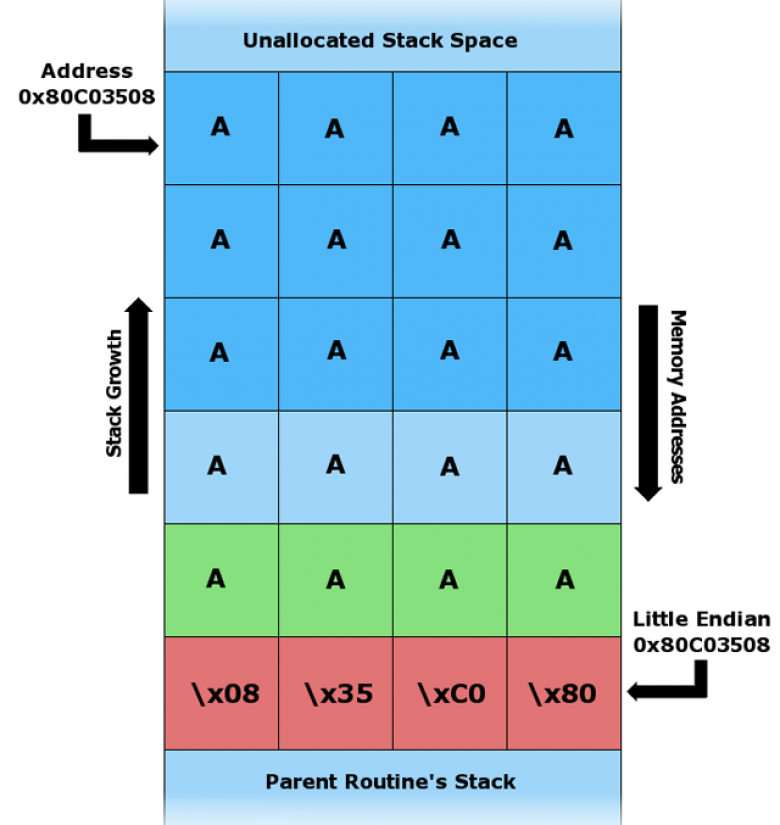
In an analysis published Monday, security researcher Jon Oberheide said Android version 4.1, aka Jelly Bean, is the first version of the Google-developed OS to properly implement a protection known as address space layout randomization. ASLR, as it's more often referred to, randomizes the memory locations for the library, stack, heap, and most other OS data structures. As a result, hackers who exploit memory corruption bugs that inevitably crop up in complex pieces of code are unable to know in advance where their malicious payloads will be loaded. When combined with a separate defense known as data execution prevention, ASLR can effectively neutralize such attacks.
Although Android 4.0, aka Ice Cream Sandwich, was the first Android release to offer ASLR, the implementation was largely ineffective at mitigating real-world attacks. One of the chief reasons for the deficiency was Android's executable region, heap, libraries, and linker were loaded at the same locations each time. This made it significantly easier for attackers designing exploits to predict where in memory their malicious code can be located.