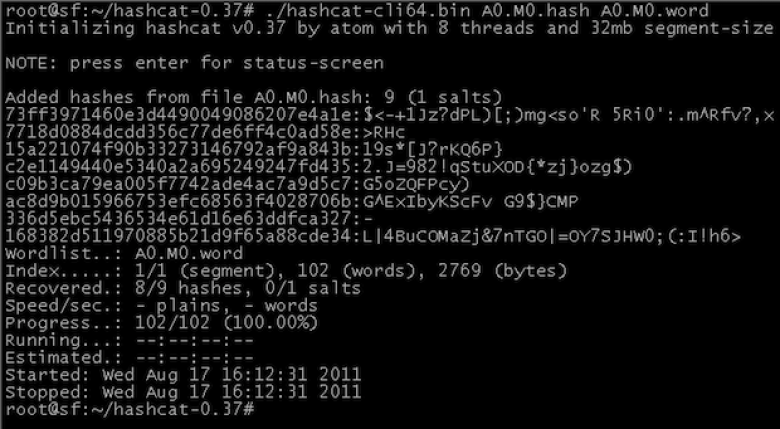
MD5 passwords 'no longer safe'
The original author of the MD5 password hash algorithm has publicly declared his software end-of-life and is “no longer considered safe” to use on commercial websites.
This comes only a day after a data breach led to 6.46 million LinkedIn hashed passwords leaking to the Web. Since the data breach, thousands of passwords, including many that could be considered strong, have been decrypted, either through brute force or through lookups.
The primary cause is LinkedIn’s failure to properly ’salt’ the hashed passwords using SHA-1 algorithm. MD5 is a password hashing algorithm similar to that of SHA-1. LinkedIn’s Vicente Silveira said on Wednesday the company has increased its security “which includes hashing and salting of our current password databases.” Although the post says this change was made “recently,” it does not indicate whether the change was applied last month, this week, or yesterday.