Active malware campaign steals Apple passwords from jailbroken iPhones
Security researchers have uncovered an active malware campaign in the wild that steals the Apple ID credentials from jailbroken iPhones and iPads.
News of the malware, dubbed "unflod" based on the name of a library that's installed on infected devices, first surfaced late last week on a pair of reddit threads here and here. In the posts, readers reported their jailbroken iOS devices recently started experiencing repeated crashes, often after installing jailbroken-specific customizations known as tweaks that were not a part of the official Cydia market, which acts as an alternative to Apple's App Store.
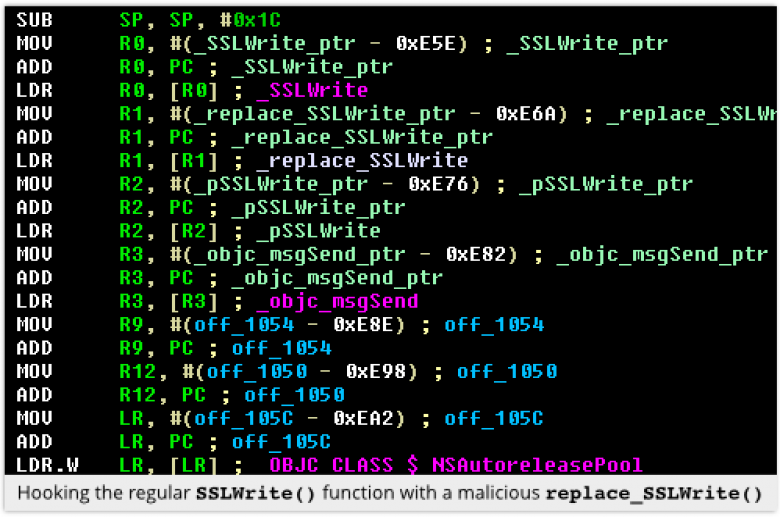
Since then, security researcher Stefan Esser has performed what's called a static analysis on the binary code that the reddit users isolated on compromised devices. In a blog post reporting the results, he said unflod hooks into the SSLWrite function of an infected device's security framework. It then scans it for strings accompanying the Apple ID and password that's transmitted to Apple servers. When the credentials are found, they're transmitted to attacker-controlled servers.