IFRAME-injecting Linux rootkit discovered
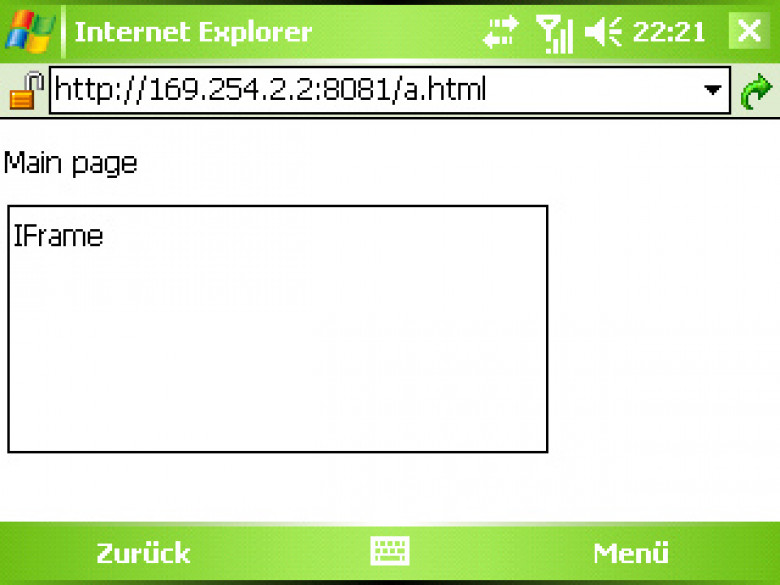
Researchers are analyzing a new rootkit that they believe signals the latest development in criminals' attempts to secretly compromise websites with the goal of directing users to exploits.
Details of the rootkit were posted anonymously Tuesday on the Full Disclosure mailing list, leading researchers from security firms CrowdStrike and Kaspersky Lab to study the malware. The anonymous poster, who runs a web service, found the rootkit on company servers after customers said they were redirected to malicious sites.
Georg Wicherski, senior security researcher at CrowdStrike, told SCMagazine.com Tuesday that it is still unknown how the 64-bit Linux rootkit got on the victim's server and how many others may have been infected by it. Researchers said the rootkit is not particularly sophisticated. But what makes it fascinating is that it hides at the kernel level to infect web servers and computers by way of watering hole tactics, or infecting sites hosted on a compromised HTTP server.